Enterprise IT teams often find themselves caught between expanding cloud environments, escalating security requirements, and a support queue that never quite clears. The tools exist, but IT complexity has outgrown internal capacity to cover it all proactively.
Most organizations respond by adding headcount or patching gaps as they appear, resulting in a reactive cycle. A system fails, a team scrambles, the incident closes, and the pattern repeats. What it rarely produces is an IT environment that prevents problems before they reach production.
Enterprises across industries are moving away from internal-only IT models toward managed IT services arrangements, where a dedicated provider maintains continuous operational coverage across infrastructure, cloud, and security under defined SLAs.
This guide walks through what managed IT services include, why enterprises use them, and how a structured engagement actually works.
What are Managed IT Services?
Managed IT services refer to the practice of outsourcing IT operations, infrastructure management, and ongoing technical support to a third-party provider known as a Managed Service Provider (MSP).
Rather than responding to problems only as they arise, an MSP delivers continuous monitoring, maintenance, security, and helpdesk support under a structured, subscription-based model.
This approach gives enterprises reliable access to specialized IT expertise across infrastructure, cloud, and security domains without building large internal teams for every function. The outcome is a more stable, secure, and cost-predictable IT environment that scales with business demand, reduces unplanned downtime, and keeps technology consistently aligned with operational and strategic goals.
Key characteristics of managed IT services:
- Subscription-based model with predictable monthly costs and defined SLAs
- Continuous 24/7 monitoring and proactive support across all covered systems
- Access to certified specialists across infrastructure, cloud, and cybersecurity
- Scalable coverage that adjusts to business needs without headcount increases
Why Enterprises Use Managed IT Services
The case for managed IT services comes down to three compounding pressures enterprise IT leaders consistently face.
- IT environments have grown significantly more complex. A single enterprise today may run workloads across multiple cloud platforms, manage dozens of SaaS applications, and maintain a hybrid infrastructure spanning data centers and remote locations.
Covering that in-house requires deep specialist coverage across multiple domains simultaneously, and most internal teams are not staffed for it.
- Qualified IT professionals across cloud, cybersecurity, and infrastructure are expensive and hard to retain. Recruiting and maintaining certified specialists across each of these domains carries a premium most organizations cannot sustain at the required depth.
- The consequences of unplanned downtime are too significant to manage reactively. System outages affect revenue, customer commitments, and regulatory standing in ways a break-fix model cannot adequately address.
According to the 2024 Gartner IT Spending Report, worldwide IT spending was projected to grow 9.3% in 2025, reflecting sustained enterprise investment as operational demands continue to expand. Managed IT services address all three pressures simultaneously.
For a global enterprise managing multi-cloud environments across geographies, an MSP provides the centralized operational layer that ensures consistent visibility, response, and reporting across every environment.
What Do Managed IT Services Include?
Managed IT services cover the full operational breadth of enterprise IT. Unlike point solutions that address isolated problems, a managed services engagement spans infrastructure, security, cloud, support, and continuity functions simultaneously.
Understanding what a comprehensive engagement typically covers helps organizations identify which gaps a managed model is best suited to address and what to expect when evaluating providers.
Infrastructure Management
Infrastructure management forms the operational backbone of any managed IT engagement. An MSP assumes responsibility for servers, endpoints, storage systems, and network hardware, ensuring each component is continuously monitored, current on patches, and performing within defined parameters.
Core activities include:
- 24/7 server and endpoint monitoring with automated alerting
- Patch management and scheduled firmware updates
- Capacity planning and storage optimization
- Hybrid IT infrastructure management across on-premises and cloud environments
The practical difference from in-house coverage is continuity. An internal team covering infrastructure during business hours will still face overnight failures and weekend outages. A managed model applies the same monitoring and response capability around the clock, regardless of when conditions emerge.
IT Support and Helpdesk Services
Enterprise helpdesk services under a managed model operate on a different logic than traditional IT support. Rather than processing tickets on a first-in, first-out basis, managed helpdesk engagements route issues to the appropriate resolution level based on complexity and business impact.
Capabilities typically included:
- Tiered L1 to L3 support covering everything from password resets to infrastructure-level incidents
- 24/7 availability with SLA-defined response times by incident priority
- Ticketing and workflow management with a full auditable record of every issue
- Structured escalation paths for recurring or complex problems
Frontline issues are handled at L1 without consuming senior engineer capacity. Complex problems escalate directly to the right expertise, reducing resolution times and preventing the same issue from cycling through an ineffective resolution path.
Network and Security Management
Network management and cybersecurity are interdependent in practice. An MSP managing enterprise networks oversees the infrastructure that connects systems while monitoring and defending against threats simultaneously.
Capabilities typically included:
- Firewall management and continuous threat detection
- Endpoint protection across all user devices and workstations
- Identity and access management (IAM)
- Vulnerability assessments and regular security testing
- Compliance monitoring aligned with ISO 27001, SOC 2, and NIST
For enterprises operating under regulatory requirements, embedding security-by-design principles into security operations makes audit preparation significantly less disruptive. Documentation exists as a continuous byproduct of normal operations rather than something assembled under pressure before an audit.
Cloud and Data Management
As enterprises shift workloads to cloud platforms, managing those environments becomes operationally complex. MSPs with cloud expertise provide the operational layer that keeps multi-cloud infrastructure performant, cost-efficient, and governed.
Scope typically includes:
- Operational support across AWS, Azure, and GCP environments
- SaaS lifecycle and workload management
- Resource provisioning and performance monitoring
- Cost optimization through cloud FinOps practices
- Data lifecycle management aligned with governance and retention policies
Cloud environments that are not actively governed accumulate unused resources and costs that compound month over month. Whether managing a cloud migration or stabilizing an existing multi-cloud footprint, a managed cloud model converts cloud spending from a variable expense into a managed, auditable line item.
Backup, Disaster Recovery, and Business Continuity
Backup and disaster recovery planning is where managed IT services deliver some of their most direct risk reduction. The difference between a well-tested recovery plan and a theoretical one only becomes clear when an incident occurs.
An MSP designs and implements recovery architectures with defined Recovery Time Objectives (RTOs) and Recovery Point Objectives (RPOs), then validates them through scheduled testing.
Core components include:
- Automated backup scheduling with geo-redundant storage
- Disaster recovery strategy design and implementation
- Business continuity planning aligned with operational risk tolerance
- Regular recovery testing and documented validation results
- Incident response playbooks for rapid activation during outage or breach scenarios
Regular testing closes the gap between what the recovery plan says and what it actually delivers.
What Managed IT Services Cover at a Glance
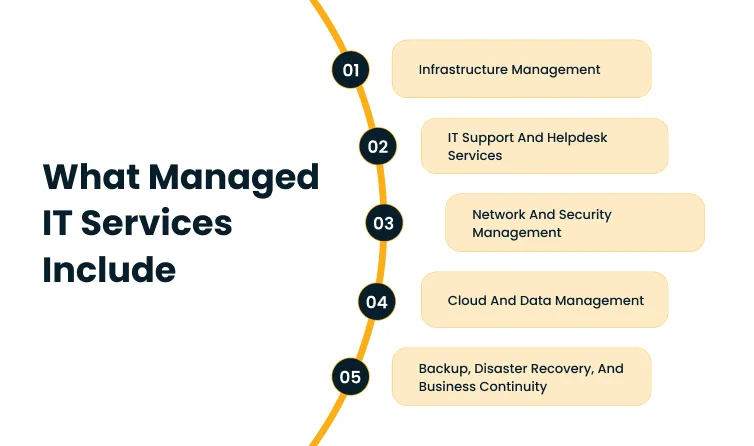
| Service Area | What It Covers |
| Infrastructure Management | Servers, endpoints, storage, 24/7 monitoring, patch management |
| IT Support and Helpdesk | Tiered L1-L3 support, SLA-backed response, ticketing |
| Network and Security | Firewalls, threat detection, IAM, compliance monitoring |
| Cloud and Data Management | Multi-cloud ops, SaaS management, FinOps, data governance |
| Backup and Disaster Recovery | Automated backups, RTO/RPO design, validated recovery testing |
Those five service areas define the operational scope of a managed engagement. The business case for each comes through most clearly in what changes once an MSP takes over.
Benefits of Managed IT Services for Enterprises
The advantages of managed IT services show up most clearly in what they change operationally. For enterprises, the shift from reactive to proactive IT management simultaneously reshapes cost structure, risk profile, and internal team focus.
Improved uptime and system reliability are among the most measurable outcomes. Proactive monitoring identifies anomalies and failure indicators before they escalate into incidents. The practical effect is that fewer problems reach users, and those that do are resolved faster.
Predictable, optimized IT costs replace the unpredictable cycle of emergency expenditure. Managed services contracts operate on fixed monthly fees, converting IT from a variable cost center into a budgeted line item.
In fact, according to the 2025 Deloitte MarginPlus study, enterprise focus on cost reduction has grown from 38% to 47% since 2024. Managed IT services align directly with this pressure by replacing reactive expenditure patterns with structured, SLA-defined operational costs.
Additional outcomes enterprises consistently report:
- Access to specialized expertise across cloud, infrastructure, and security domains, giving enterprises depth in areas where recruiting full-time specialists is cost-prohibitive.
- Stronger security and compliance posture built through continuous monitoring, automated patching, and proactive threat detection, with cloud infrastructure security and compliance alignment embedded into ongoing operations across ISO 27001, SOC 2, and NIST.
- Scalability is aligned with business growth, allowing IT capacity to expand or contract without proportional headcount adjustments.
- Reduced internal IT workload, enabling teams to focus on strategic priorities rather than routine maintenance and incident response.
- Faster incident resolution through automated alerting, structured escalation, and SLA-defined response commitments that limit downstream business impact.
These outcomes compound over time, reframing managed IT as an operational foundation.
How Managed IT Services Work in Practice
Understanding the managed IT lifecycle helps set realistic expectations for onboarding, ongoing operations, and long-term improvement.
A well-structured engagement starts with a systematic assessment of the current environment, progresses through structured implementation, and evolves into an ongoing partnership where performance is measured, reported, and continuously improved against agreed benchmarks. Let’s take a look at how that works in practice.
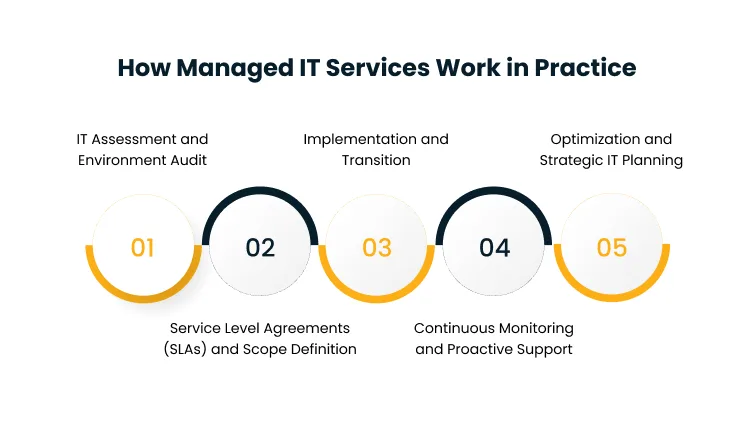
1. IT Assessment and Environment Audit
Before any services are delivered, the MSP conducts a detailed assessment of the existing IT environment.
The assessment covers:
- Full inventory and documentation of current systems, applications, and infrastructure
- Identification of existing risks, vulnerabilities, and operational inefficiencies
- Gap analysis comparing current capabilities against required performance levels
- Mapping of IT systems to critical business processes and dependencies
The output is the foundation for every service design, SLA commitment, and monitoring configuration that follows. Engagements that skip this phase frequently encounter coverage gaps mid-operation, recreating the reactive conditions that managed IT is designed to replace.
2. Service Level Agreements (SLAs) and Scope Definition
SLAs are the operational contracts that define what the MSP is responsible for, how performance is measured, and what the enterprise can expect in terms of response and resolution.
Key elements include:
- Uptime guarantees by system tier (for example, 99.9% availability for business-critical systems)
- Response and resolution time commitments by incident priority
- Explicit scope definition covering inclusions and exclusions
- Compliance and reporting requirements aligned with the enterprise’s regulatory environment
Without clear performance benchmarks and defined responsibilities, there is no basis for measuring whether the engagement is delivering value.
3. Implementation and Transition
Moving from internal IT management to a managed services model requires careful sequencing to avoid disrupting operations during handover.
Transition activities typically include:
- Migration of monitoring and management tooling to the MSP’s platform
- Integration of enterprise systems into the MSP’s ticketing and workflow environment
- Knowledge transfer covering system configurations, historical incidents, and operational dependencies
- Parallel running periods where both teams operate together before full handover
Organizations pursuing cloud modernization services in parallel with transition should allow additional time in this phase. Running both teams simultaneously surfaces undocumented dependencies that would otherwise create gaps post-handover.
4. Continuous Monitoring and Proactive Support
Continuous monitoring is where the shift from reactive to proactive IT support becomes operational. Once live, the MSP applies real-time surveillance across every covered system and intervenes before conditions escalate into user-facing incidents.
Activities at this phase include:
- Real-time infrastructure and application monitoring using AI-driven tools
- Automated alerting for anomalies, threshold breaches, and potential failure conditions
- Proactive intervention to resolve emerging issues before they affect users
- Regular security scans, patch deployment, and system health reviews
For enterprises moving from a reactive model, the results become visible quickly. Fewer escalations, faster resolution, and a support queue that reflects genuine edge cases rather than recurring systemic problems.
5. Optimization and Strategic IT Planning
A mature managed IT engagement does not plateau at stable operations. Over time, it evolves into a strategic partnership where the MSP contributes to IT planning alongside enterprise leadership.
This phase covers:
- Quarterly performance reviews with data on uptime, incident patterns, and SLA adherence
- Cost optimization reviews identify licensing inefficiencies, underutilized infrastructure, or workflow redundancies
- IT roadmap alignment connecting technology investments to business initiatives
- Architecture and capacity recommendations informed by operational performance data
The lifecycle framework, “Assess, Define, Implement, Monitor, Optimize,” reflects how structured managed services engagements build cumulative resilience rather than simply maintaining the status quo.
Providers like Cygnet.One support this full lifecycle through continuous monitoring, proactive support, and long-term IT planning that aligns each enterprise’s technology operations with its compliance requirements and strategic direction.
Conclusion
Enterprises that manage IT reactively spend more time recovering from problems than planning for growth. This is why identifying where your current IT environment has the most coverage gaps is the starting point.
If you work with Cygnet.One, you get:
- 24/7 monitoring and SLA-backed support across infrastructure, cloud, and security
- Proactive incident detection and structured escalation paths
- Compliance alignment embedded into ongoing operations
What makes this model work is the shift from incident response to operational continuity. Internal teams regain the bandwidth to focus on what actually moves the business forward. If you want to explore what a managed IT engagement looks like for your organization, book a demo with Cygnet.One today.
FAQs
Managed IT services are proactive and ongoing, where an MSP continuously monitors, maintains, and supports IT infrastructure under a subscription model with defined SLAs. IT outsourcing is typically reactive and project-based, addressing specific tasks or capacity gaps rather than continuous operational coverage. The core distinction is continuity of service and structured performance accountability.
Managed IT services are particularly well-suited for large enterprises managing complex, multi-cloud, or geographically distributed IT environments. The scale and specialization required across cloud, cybersecurity, infrastructure, and compliance align closely with what a structured MSP delivers. Larger organizations see the clearest returns in cost predictability and operational depth.
Managed IT services improve security through continuous monitoring, threat detection, regular patching, and alignment with compliance requirements. An MSP provides round-the-clock surveillance across endpoints, networks, and access controls, enabling faster threat detection than most internal teams can sustain. ISO 27001, SOC 2, and NIST are embedded into ongoing operations rather than addressed only at audit time.
A typical SLA includes uptime guarantees by system tier, response and resolution time commitments by incident priority, a clearly defined service scope, and agreed performance metrics. SLAs may also include compliance reporting obligations relevant to the enterprise’s regulatory environment, making them both an operational instrument and a governance framework.
Managed IT services reduce downtime through proactive monitoring, automated alerting, and structured incident response that identifies failure conditions before they reach users. The MSP’s monitoring infrastructure flags anomalies in real time rather than waiting for user reports. SLA-backed response commitments and documented escalation paths reduce both the frequency and duration of outages.
Choose a provider based on technical certifications, SLA clarity, depth of experience across your environment, and the ability to operate as a strategic partner. Key criteria include performance reporting transparency, engagement scalability, security capabilities, and demonstrated outcomes from comparable enterprise clients.