Cloud migration offers scalability, cost efficiency, and operational flexibility that on-premises infrastructure rarely matches. However, the transition itself is one of the most technically complex initiatives an organization can undertake.
Many businesses move forward with migration plans without fully accounting for the risks involved, and the consequences range from cost overruns and service disruptions to compliance violations and data loss.
Understanding cloud migration challenges is a prerequisite for execution.
The organizations that navigate migration successfully are not the ones with the largest budgets or the most advanced technology stacks. They are the ones who identified risks before migration began, built plans that accounted for those risks, and executed in a sequence that kept exposure manageable at every stage.
This blog breaks down the most common cloud migration challenges, explains how to surface risks before they become problems, examines why migrations fail when planning is absent, and provides a structured step-by-step strategy that organizations can apply regardless of their starting point.
Top Cloud Migration Challenges
Cloud migration introduces a set of challenges that appear across migrations of all sizes and at all levels of organizational maturity.
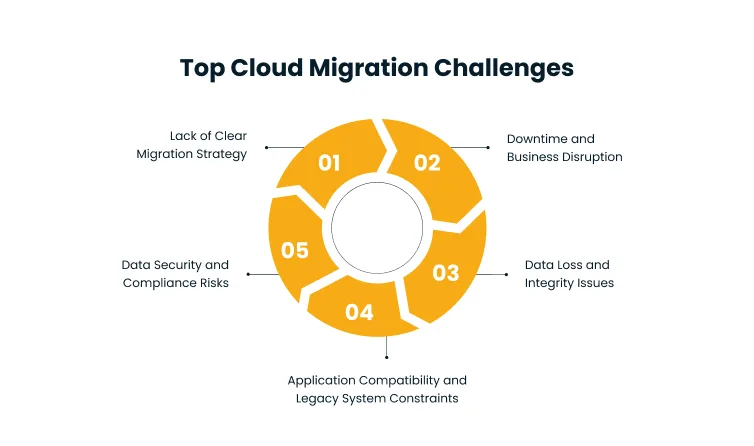
Understanding each one in detail is the starting point for building a migration plan that does not simply move workloads from one environment to another, but does so without compromising security, continuity, or data integrity.
1. Lack of a Clear Migration Strategy
The most common reason cloud migrations stall or fail is the absence of a clearly defined migration strategy before execution begins.
Organizations often approach migration as a technical project with a start date and an end date, without investing the time to map out what is being moved, in what order, under what constraints, and with what success criteria.
Without a defined roadmap, teams face overlapping responsibilities, conflicting priorities, and repeated scope changes mid-execution. Decisions that should have been made before migration begins are made under pressure during it, and those decisions are rarely the right ones.
Workloads that should have been migrated last get moved first. Dependencies that were not mapped cause downstream failures. Timelines stretch as teams rework what should have been planned.
A migration strategy is not a high-level intention to move to the cloud. It is a document that specifies which workloads are in scope, which cloud provider and deployment model will be used, what the migration sequence is, who owns each phase, and how success will be measured.
Without it, migration complexity scales faster than the team’s ability to manage it.
2. Data Security and Compliance Risks
Data is at its most vulnerable during migration. The moment data leaves on-premises systems and moves across networks to a cloud environment, it is exposed to interception, misconfiguration, and unauthorized access in ways that do not exist in a stable, static infrastructure.
Organizations that fail to establish security controls before migration begins often discover compliance gaps only after sensitive data has already been moved.
Regulatory requirements add another layer of complexity. Industries operating under GDPR, HIPAA, SOC 2, or PCI DSS face strict rules about where data can be stored, how it must be encrypted, and who can access it.
A cloud environment that is technically functional but non-compliant creates legal and financial exposure that can exceed the cost of the migration itself.
Common security risks include:
- Unencrypted data in transit between on-premises and cloud environments
- Misconfigured cloud storage buckets or access policies during setup
- Inadequate identity and access management controls post-migration
- Failure to audit third-party integrations and their data access permissions
Security planning must begin before migration does. Every workload category requires a security assessment that accounts for data sensitivity, applicable regulations, and the specific controls required in the target cloud environment.
3. Downtime and Business Disruption
Migrating live systems creates a risk of service interruption. Even migrations that are technically executed correctly can cause downtime if they are not sequenced carefully, tested thoroughly, and timed to minimize impact on business operations.
For customer-facing systems, operational platforms, or revenue-generating applications, downtime during migration is not an acceptable outcome.
Downtime risk is amplified when teams underestimate the complexity of interdependencies between systems.
Migrating a database without accounting for every application that queries it, or moving an application without ensuring its authentication service is available in the new environment, introduces failure points that are difficult to diagnose and expensive to recover from under operational pressure.
The organizations that manage downtime risk most effectively do so through planning rather than speed. They schedule migrations during low-traffic periods, test failover procedures in advance, maintain rollback options for every critical system, and stage migration in phases that isolate failure risk to a small portion of the infrastructure at any given time.
4. Data Loss and Integrity Issues
Data loss during migration is more common than most organizations expect. Incomplete transfers, format conversions that introduce errors, synchronization gaps when live data is being moved, and configuration mistakes in the target environment can all result in data that arrives corrupted, incomplete, or out of sequence.
In some cases, data loss is not discovered until weeks after migration completes, at which point reconstruction is costly and may be impossible.
Data integrity issues are particularly dangerous for organizations where historical records, transaction logs, or customer data represent the operational backbone of the business.
A financial services firm that migrates five years of transaction data and discovers, post-migration, that three months of records are corrupted faces a recovery challenge that can cascade into regulatory and customer trust issues.
Preventing data loss requires validation at every stage of migration:
- Pre-migration checksums establish a baseline for comparison.
- Mid-migration monitoring catches transfer errors in real time.
- Post-migration validation confirms that destination data matches source data before systems are decommissioned.
5. Application Compatibility and Legacy System Constraints
Not every application is cloud-ready. Legacy systems built for on-premises environments frequently depend on hardware configurations, network architectures, or software stacks that do not translate cleanly into cloud infrastructure.
Forcing these systems into a cloud environment without modification often results in performance degradation, integration failures, or functionality gaps that require expensive remediation.
Common compatibility issues include applications that rely on specific operating system versions no longer supported in cloud environments, database systems that lack native cloud connectors, and monolithic architectures that cannot be horizontally scaled.
In some cases, the cost of refactoring a legacy application for cloud compatibility exceeds the cost of replacing it entirely.
Addressing application compatibility requires a thorough assessment before migration begins.
Each application should be evaluated against a standardized framework that identifies whether it can be lifted and shifted as-is, needs re-platforming with minimal code changes, requires refactoring for cloud-native capability, or should be replaced with a SaaS alternative.
Attempting to migrate applications without this classification leads to discoveries mid-migration that halt progress and inflate costs.
How to Identify Cloud Migration Risks Early
Early risk identification does not require predicting every possible failure. It requires building processes that surface the most likely failure points before they have a chance to materialize.
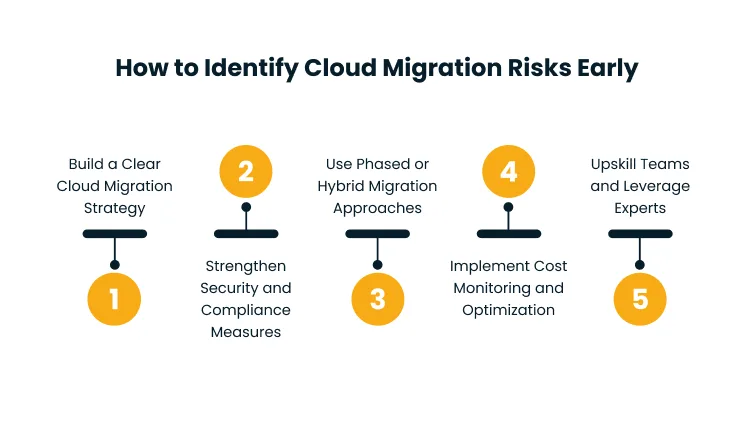
The five practices below address the risk categories that account for the majority of cloud migration failures.
1. Build a Clear Cloud Migration Strategy
The migration strategy is the primary tool for early risk identification. When objectives, scope, timelines, workload sequencing, and success criteria are defined upfront, the gaps and conflicts that would otherwise surface mid-migration become visible during planning.
Dependencies that were not obvious become apparent when workloads are mapped in sequence. Resource constraints become visible when timelines are set against team capacity. Regulatory requirements surface when workload categories are defined.
A migration strategy that is detailed enough to identify risks typically includes a full workload inventory, a migration wave plan that sequences workloads by dependency and risk level, a defined testing protocol for each migration phase, an owner for each workload and phase, and explicit rollback procedures for critical systems.
Building this level of detail is time-consuming, but the investment consistently reduces execution risk.
2. Strengthen Security and Compliance Measures
Security risks that are not identified before migration begins are the hardest to remediate after it ends.
Data that has already been moved to a non-compliant configuration, access policies that were not reviewed before systems went live, or encryption that was not applied during transfer cannot be retroactively secured without significant operational disruption.
Early security risk identification requires a structured pre-migration assessment that covers three areas.
- First, classify all data by sensitivity and applicable regulatory requirements before any workload moves.
- Second, define the access control model for the target cloud environment before provisioning begins.
- Third, audit every third-party integration that will connect to migrated systems and confirm that its data access permissions meet the organization’s security standards.
Organizations subject to specific regulatory frameworks should engage compliance reviewers before migration begins.
Identifying a HIPAA compliance gap after a healthcare database has been migrated is a significantly more expensive problem than identifying it during the pre-migration security assessment.
3. Use Phased or Hybrid Migration Approaches
Phased migration reduces risk by limiting the scope of any single migration event. Rather than moving the entire infrastructure at once, a phased approach sequences workloads into waves, starting with lower-risk systems and using each phase as a learning exercise that informs the next one.
Issues discovered in phase one, whether technical, operational, or process-related, are corrected before phase two begins, compounding the error reduction with each successive wave.
Hybrid migration approaches maintain parallel operation of on-premises and cloud environments during the transition period.
This provides a fallback for critical systems if migration issues arise and allows organizations to validate that cloud-hosted systems perform correctly under real operational conditions before decommissioning the on-premises versions.
The phased or hybrid approach is particularly valuable for organizations migrating mission-critical systems where any disruption to availability carries high business cost.
The additional time required by a phased approach is consistently less than the recovery time required when a full-scale migration encounters significant problems.
4. Implement Cost Monitoring and Optimization
Cloud cost overruns are one of the most frequently reported cloud migration problems. Organizations that migrate without establishing cost monitoring and governance controls often discover that cloud spend significantly exceeds projections, sometimes by multiples.
The cloud’s pay-as-you-use model creates cost exposure that on-premises fixed infrastructure does not.
Early cost risk identification requires estimating cloud consumption before migration begins, establishing budgets for each migration phase, and deploying cost monitoring tools before any workload goes live.
Organizations should define cost thresholds that trigger review before provisioning decisions are made, and assign ownership of cloud cost to specific teams rather than treating it as a shared and unmanaged operational expense.
5. Upskill Teams and Leverage Experts
Most cloud migration failures have a skills component. Teams that have managed on-premises infrastructure for years do not automatically have the cloud expertise required to design, execute, and operate a cloud environment.
Security configurations that are straightforward in a cloud-native context are non-obvious to engineers whose experience is primarily on-premises. Cost management tools, identity and access management systems, and cloud networking architectures all require cloud-specific knowledge to implement correctly.
Risk identification should explicitly assess team capability gaps before migration begins. Where gaps exist, the response should be a combination of structured training, hiring, and external expert engagement.
Using experienced migration partners for high-risk phases is not an admission of internal capability failure. It is a deliberate risk management decision that reduces the probability of the most expensive failures.
Why Cloud Migration Fails Without Proper Planning
Cloud migrations do not fail because the cloud is unreliable. They fail because the organizations executing them did not invest sufficiently in preparation before execution began.
The technical capability to migrate exists. The failure point is almost always in the planning that precedes the technical work.
Underestimating complexity is the most common planning failure. Organizations that assess their migration scope at a high level miss the dependencies, edge cases, and legacy constraints that become major problems once migration is underway.
A workload that looks simple from the outside may have undocumented integrations with eight other systems. A database that appears portable may have performance characteristics that degrade significantly in a cloud environment without tuning.
These discoveries surface during execution for organizations that did not surface them during planning.
Unclear objectives compound the problem. Migrations that begin without defined success criteria have no mechanism for evaluating whether they are proceeding correctly.
Teams optimize for speed rather than stability. Workloads that should be tested thoroughly get moved quickly to meet deadlines, and the problems that testing would have caught manifest instead in production.
Coordination failures are the third common cause. Cloud migration involves network, security, application, database, and operations teams all working on interdependent tasks.
When these teams do not share a unified plan, changes made by one team create problems for another.
A network configuration change that fixes one workload’s connectivity breaks another’s. A security policy applied to a storage layer blocks an application team’s access.
Without a coordinated plan that all teams are working from, these conflicts are discovered in real time rather than resolved in advance.
According to Gartner’s analysis of cloud migration outcomes, most cloud migrations that fail do so for organizational and planning reasons, not technical ones. The technology works, but the planning does not.
Cloud Migration Strategy: Step-by-Step Guide
A structured migration strategy converts the complexity of cloud migration into a manageable sequence of well-defined steps. Each step below builds on the previous one, and skipping any step increases the risk carried into subsequent stages.
Organizations with straightforward migrations may move through some steps quickly. Organizations with complex legacy environments or strict compliance requirements will invest more time in the early steps, and that investment will reduce execution risk proportionally.
Step 1: Define Business Goals and Migration Objectives
Migration without defined business goals is an infrastructure project in search of a purpose. Before any technical assessment begins, the organization must establish what it is trying to achieve through migration.
Cost reduction, improved scalability, enhanced disaster recovery capability, faster development cycles, and regulatory compliance are all legitimate migration drivers, but each one implies different architecture decisions, workload prioritization, and success criteria.
Business goals should be translated into specific, measurable migration objectives. If the goal is cost reduction, define the target reduction and the timeline for achieving it.
If the goal is scalability, define the workload growth that the new environment must support. Objectives that cannot be measured cannot be managed, and migrations without measurable objectives consistently drift in scope and cost.
Step 2: Assess Your Current Infrastructure and Applications
A thorough infrastructure and application assessment is the foundation for every subsequent step in the migration strategy. This assessment maps every workload, application, database, integration, and dependency in the current environment.
It identifies which systems are cloud-ready, which require modification, and which represent compatibility or compliance risk.
The assessment should produce a complete inventory rather than a representative sample. Gaps in the inventory become surprises during migration.
Every application should be documented with its current hardware dependencies, operating system requirements, network configuration, data storage footprint, integration touchpoints, and performance requirements.
This documentation becomes the reference point for migration planning and the basis for workload classification.
Step 3: Identify Workloads to Migrate First
Migration sequencing matters as much as migration methodology. Starting with the wrong workload creates unnecessary risk and can undermine organizational confidence in the migration program before it reaches the systems where migration value is highest.
The standard approach is to prioritize workloads that are low-risk and cloud-compatible for initial migration waves. These workloads validate the migration process, build team familiarity with the cloud environment, and demonstrate progress without exposing the organization to high-consequence failures.
High-risk or business-critical workloads should be sequenced later, after the team has validated its tooling, processes, and cloud environment configuration on lower-stakes systems.
Workload selection should account for business impact, technical complexity, dependency chains, and compliance requirements. Workloads with many dependencies should be grouped to migrate together or sequenced carefully to ensure that dependencies are available in the target environment before dependent systems move.
Step 4: Build a Detailed Migration Roadmap
The migration roadmap is the operational document that guides execution. It translates the workload inventory and sequencing decisions into a time-phased plan with defined milestones, resource assignments, and risk mitigation procedures at each stage.
A functional migration roadmap includes migration waves with defined scope and timing, owner assignments for each workload and phase, dependencies mapped between waves to prevent sequencing errors, testing requirements and validation criteria for each phase, rollback procedures for each critical workload, and escalation paths for issues that exceed the team’s authority to resolve.
The roadmap should be a living document that is updated as each phase completes and learning is incorporated. The plan built before migration begins will not survive contact with execution unchanged.
Building update mechanisms into the roadmap from the start prevents the plan from becoming a historical artifact rather than an operational guide.
Step 5: Evaluate Security, Compliance, and Governance Requirements
Every workload in the migration scope should be evaluated against the security and compliance requirements applicable to it before it moves. This step produces the security architecture for the target cloud environment and defines the controls that must be in place before each workload category can be migrated.
Security evaluation should cover:
- Data classification and encryption requirements
- Identity and access management design
- Network segmentation and firewall configuration
- Audit logging and monitoring requirements, and
- Incident response procedures specific to the cloud environment.
Compliance evaluation should map each applicable regulatory framework to the controls required in the target environment and confirm that the cloud provider’s compliance certifications cover the organization’s specific requirements.
Governance requirements define how cloud resources will be provisioned, managed, and monitored on an ongoing basis. Establishing governance before migration rather than after prevents the accumulation of ungoverned cloud resources, which creates security and cost exposure over time.
Step 6: Prepare Data, Applications, and Dependencies
Preparation is the step between planning and execution. It involves making the specific changes to data, applications, and configurations required for a successful migration before the migration itself begins.
Data preparation includes:
- Cleansing records that will not migrate cleanly
- Resolving data quality issues that could corrupt the destination environment
- Establishing baseline checksums for validation, and
- Designing the synchronization approach for data that will continue to change during migration.
Application preparation includes refactoring or re-platforming applications identified during assessment as incompatible with the target cloud environment, updating configurations to reference cloud-compatible endpoints, and testing application functionality in a cloud environment that mirrors the target.
Dependency preparation involves ensuring that every system a migrating workload depends on will be available in the target environment at the time of migration.
Step 7: Select the Right Cloud Tools and Migration Partners
Cloud migration involves a range of tooling decisions across infrastructure provisioning, data transfer, application deployment, monitoring, and cost management. The tools selected should align with the specific workload types, cloud provider, and team capability in the migration plan.
Selecting tools that the team does not have the expertise to operate introduces its own category of risk.
Migration partner selection follows similar logic. Partners should be evaluated on their direct experience with the specific cloud provider, workload types, and industry compliance requirements applicable to the organization.
Reference checks from organizations that have executed comparable migrations are more reliable than capability claims in proposal documents.
Cygnet.One’s cloud migration services are designed for organizations that need end-to-end migration support, from pre-migration assessment through post-migration optimization, with built-in compliance and security controls for regulated industries.
Step 8: Run a Pilot Migration and Validate Performance
A pilot migration tests the migration process, tooling, and cloud environment configuration on a real but limited scope workload before full-scale migration begins. The pilot is not a proof of concept. It is a full execution of the migration process against a representative workload, with all security controls, monitoring, and validation procedures active.
The pilot should be selected for its representativeness. A workload that is too simple to surface integration or performance issues does not generate useful learning.
After the pilot migration completes, validate that the workload performs at or above its pre-migration baseline, that all integrations function correctly, and that security and compliance controls are operating as designed.
Issues discovered during the pilot should be documented, root-caused, and resolved before the next migration wave begins. The learning value of the pilot is only realized if its findings are systematically incorporated into the migration plan before execution continues.
Step 9: Execute the Full Migration in Phases
Full migration execution follows the roadmap built in step four, with the refinements incorporated after the pilot. Each wave moves the workloads assigned to it according to the defined sequence, with validation occurring between waves before the next one begins.
Phased execution keeps risk contained. If an issue surfaces during a migration wave, it affects only the workloads in that wave. The issue can be investigated and resolved before migration continues, and any necessary changes to the process or tooling can be made before more workloads are exposed.
Communication is critical during execution. Teams, stakeholders, and affected business units should know what is being migrated and when.
Surprises during migration undermine confidence and generate support volume that consumes engineering time. Proactive communication about migration schedules, expected impacts, and rollback procedures reduces this friction significantly.
Step 10: Monitor, Optimize, and Troubleshoot Post-Migration
Migration completion is not the end of the migration program. The first weeks after each migration wave are the period when issues that were not caught during testing surface under real operational load.
Post-migration monitoring must be active before workloads go live in the new environment, not set up after problems are reported.
Monitoring should cover application performance, database query performance, network latency, error rates, security event logs, and cloud cost.
Establishing baselines from the pilot migration provides a reference point for identifying anomalies after full migration. Performance degradation, unexpected cost spikes, or unusual security events in the post-migration period are signals that require investigation rather than normalization.
Optimization is ongoing. Cloud environments are not static, and the configuration that performs well on day one may not be optimal six months later as workload patterns evolve.
Establishing a regular review cadence for performance, cost, and security ensures that the cloud environment continues to deliver the value the migration was designed to create.
Step 11: Train Teams and Establish Ongoing Cloud Management
A successfully migrated cloud environment requires ongoing management by teams with cloud-specific expertise. The skills required to operate a cloud environment differ from those required to operate an on-premises infrastructure, and the gap is significant enough to create operational risk if it is not addressed before migration completes.
Training should be role-specific. Operations engineers need cloud infrastructure management skills. Security teams need cloud security monitoring and incident response skills.
Finance and operations stakeholders need cloud cost management skills. Development teams need cloud-native development and deployment skills. Generic cloud training programs rarely address the specific tools, configurations, and workflows relevant to the organization’s environment.
Ongoing cloud management requires defined ownership, governance processes, and regular review cadences that keep the cloud environment aligned with the organization’s security, cost, and performance requirements.
Organizations that complete migration without establishing these ongoing management structures often find that their cloud environment drifts toward a state that is more expensive, less secure, and less well-governed than the on-premises environment it replaced.
Conclusion
Cloud migration can unlock significant and durable business value. Reduced infrastructure costs, improved scalability, faster deployment cycles, and better disaster recovery capability are all achievable outcomes, but they are not automatic.
The gap between a migration that delivers these outcomes and one that results in cost overruns, security incidents, and operational disruption is almost always a planning gap.
Organizations that approach migration as a strategic initiative, with defined objectives, structured risk identification, phased execution, and ongoing management investment, consistently achieve better outcomes than those that treat it as a technical project with a delivery date.
The eleven steps in this guide provide a framework for building that kind of migration program, from the business goal definition that gives the migration its purpose to the ongoing cloud management practices that protect its value over time.
A well-executed cloud migration is the foundation of a cloud operating model that evolves as the business does. Organizations that build that foundation correctly the first time spend less time and money maintaining it over the years that follow.
Cloud migration complexity scales quickly without the right expertise in place. Cygnet.One’s cloud migration and modernization services help enterprises build the migration strategy, security architecture, and cloud management model required to move complex workloads without disruption.
Book a demo with the Cygnet.One team about where your migration program stands and what it takes to move forward with confidence.
Frequently Asked Questions
Security risks, downtime, data loss, application compatibility issues, and the absence of a clear migration strategy are the most consistently reported cloud migration challenges. Security and compliance risks are particularly consequential because they can produce legal and financial exposure that outlasts the migration itself. Downtime and data loss carry immediate operational impact.
Cloud migration most commonly fails due to inadequate planning, lack of cloud expertise within the migration team, and failure to map and account for system dependencies before execution begins. Underestimating workload complexity and skipping validation steps to accelerate timelines are also significant contributors.
Cloud migration risks are most effectively reduced through a combination of phased migration, pre-migration security and compliance assessment, thorough workload dependency mapping, pilot testing before full-scale execution, and team capability development.
A phased migration strategy with clearly defined business objectives, thorough pre-migration assessment, wave-based workload sequencing, pilot validation before full-scale execution, and continuous monitoring throughout is the approach that consistently produces the best outcomes. There is no single strategy that is optimal for every organization, but the elements above are present in virtually every successful migration regardless of scale, industry, or cloud provider.
Cloud migration timelines vary significantly based on the scope of the migration, the complexity of the workloads involved, and the organization’s starting level of cloud readiness. Simple migrations involving a small number of cloud-compatible workloads can be completed in weeks. Migrations involving complex legacy systems, large data volumes, or strict regulatory requirements typically take months. Enterprise-wide migrations that include application refactoring or re-architecture can take a year or more to complete fully.