Introduction
Financial institutions manage some of the most sensitive data in existence — transaction records, customer financials, loan portfolios, tax filings — and a single recovery failure can trigger regulatory penalties, client losses, and operational collapse. According to IBM's 2025 Cost of a Data Breach Report, the average breach cost for the financial services sector reached USD 5.56 million, significantly higher than the global average of USD 4.44 million.
With ransomware attacks, insider threats, and infrastructure failures hitting financial institutions at growing rates, robust backup and disaster recovery strategies are now both regulatory requirements and core business continuity tools.
This article covers the unique backup challenges financial institutions face, the types of backup and disaster recovery methods available, regulatory compliance requirements across India, the UAE, Saudi Arabia, and the UK, and actionable best practices to build a resilient data protection strategy.
TLDR
- Financial institutions face stricter backup requirements due to regulatory mandates, breach costs, and zero tolerance for downtime
- Frameworks like SOX, PCI DSS, GDPR, DPDP Act, and SAMA define specific data retention and protection standards
- The 3-2-1 rule — three copies, two media types, one offsite — is the industry-standard starting point
- RTOs and RPOs must be clearly defined; Tier 1 financial systems typically require recovery within minutes
- Encryption, immutable backups, access controls, and regular testing are non-negotiable for financial-grade protection
Why Financial Services Demands Specialized Backup & Disaster Recovery
Financial services ranks as one of the most heavily targeted sectors for cybercrime. The Verizon 2025 Data Breach Investigations Report documented 3,336 security incidents in the Finance & Insurance sector, with 927 confirmed breaches — a clear indication that financial institutions face relentless attack pressure from ransomware operators, insider threats, and state-sponsored actors.
Data Categories Requiring Protection
Financial institutions must protect multiple categories of highly sensitive data, each carrying distinct retention obligations:
- Customer account records and personally identifiable information (PII)
- Loan and credit files with complete application histories
- Transaction histories across all channels and systems
- Tax compliance records including e-invoices, GST filings, and VAT records
- Complete audit trails for regulatory examination
- Employee data and internal financial records
The Cascade of Consequences
Data loss in financial services creates consequences far beyond IT disruption. Organizations face regulatory investigations, inability to prove compliance during audits, frozen operations for NBFCs and payment processors, and loss of client trust that can take years to rebuild. The TSB Bank incident in the UK resulted in a £48.65 million fine from the FCA and PRA for IT migration failures that included inadequate disaster recovery arrangements.
The Financial Sector Threat Landscape
Financial institutions face specific threats that demand specialized backup strategies:
- Ransomware attacks that encrypt customer records and demand payment before decryption
- Insider threats with privileged access to financial systems and backup infrastructure
- Natural disasters or infrastructure failures that can take core banking systems offline
- Supply-chain attacks targeting vendors and service providers, as seen in the 2024 C-Edge Technologies ransomware incident that temporarily blocked nearly 300 Indian cooperative banks from UPI and retail payment systems

Data Integrity in the Financial Context
Financial institutions need recovered data that is accurate, untampered, and auditable — not just available. This matters especially for e-invoices, GST reconciliations, and tax filings, where regulators may scrutinize historical records years after they were created.
That compliance burden shapes what financial institutions should demand from their technology partners. Cygnet.One, operating as a GSTN-approved IRP and GST Suvidha Provider, processes millions of financial transactions monthly under strict data integrity requirements — demonstrating the compliance standard that backup and recovery infrastructure must meet in this sector.
The 4 Types of Data Backup Financial Institutions Should Know
Not all backup methods serve the same purpose. Financial institutions typically combine multiple types to balance recovery speed, storage costs, and regulatory requirements. Here's how each approach works — and where it fits.
Full Backup
A full backup copies all data in its entirety at a single point in time. It offers the simplest recovery path but requires the most storage space and time to complete. Financial institutions typically schedule full backups weekly or monthly, supplemented by more frequent incremental or differential backups.
Best for: Weekly or monthly baseline snapshots, regulatory archive requirements, systems with manageable data volumes.
Incremental Backup
Incremental backups only copy data that has changed since the last backup (whether full or incremental). This dramatically reduces backup time and storage costs. The tradeoff: recovery requires rebuilding from multiple backup sets — the last full backup plus each incremental — which can extend restoration time during an incident.
Best for: Daily backups of high-volume transaction systems, environments where storage efficiency is critical, systems with frequent small changes.
Differential Backup
Differential backups copy all data changed since the last full backup, striking a middle ground between full and incremental. Recovery is faster than incremental (only two sets needed: the last full plus the latest differential), making it a good fit for financial systems where recovery speed is critical.
Best for: Systems requiring faster recovery than incremental can provide, mid-sized datasets with moderate change rates, balancing storage efficiency with recovery speed.
Cloud and Hybrid Backup
Modern financial institutions increasingly use cloud or hybrid backup models: encrypted backups stored offsite in the cloud, with local copies retained for fast recovery. This approach directly supports the 3-2-1 rule and enables the geographic data redundancy needed for multi-jurisdiction operations.
Best for: Meeting offsite backup requirements, geographic redundancy, scalable storage capacity, supporting disaster recovery across multiple locations.
In practice, most financial institutions don't rely on a single backup type. A typical production environment combines weekly full backups, daily incrementals, and cloud-based offsite copies — layered to satisfy both recovery time targets and compliance mandates. The next section examines how to structure these layers into a complete disaster recovery strategy.

Regulatory Compliance: The Non-Negotiable Backbone
Financial institutions don't get to choose whether compliance shapes their backup strategy — it defines the floor. Backup policies must align with multiple overlapping regulatory frameworks depending on geography and business type, and the penalties for falling short are measurable.
Key Compliance Frameworks
Global and multi-jurisdictional:
- SOX (Sarbanes-Oxley): Mandates 7-year retention for audit and review records related to financial reporting integrity
- PCI DSS v4.0: Requires data minimization for cardholder data with business-justified retention periods and secure deletion protocols
- GDPR (Europe): Enforces storage limitation principles with exemptions for legal compliance obligations
India:
- DPDP Act 2023: Establishes purpose-based retention with sector-specific overrides
- RBI IT Governance Framework: Requires minimal RTO and near-zero RPO for critical systems
- GST Rules (Section 36 CGST Act): Mandates 72-month (6-year) retention for GST records and e-invoices
Middle East:
- UAE CBUAE: Requires minimum 5-year retention for all records
- Saudi Arabia SAMA Cybersecurity Framework: Mandates formal backup management strategy including offline backups
United Kingdom:
- FCA/PRA Operational Resilience: Requires firms to define impact tolerances and validate through testing
Data Retention Obligations
Most frameworks require financial transaction records and customer data to be retained for a minimum of 5-7 years. Key retention minimums by jurisdiction include:
- India (GST/e-invoices): 6 years (72 months) from the annual return's due date
- UAE CBUAE: 5 years for all records
- SOX (US): 7 years for audit and financial reporting records
- GDPR (EU): Varies by purpose; legal compliance exemptions apply

Backup strategies must account for these long-tail obligations — including immutable storage that prevents tampering or premature deletion.
Immutable Backups for Financial Services
In financial services, the integrity of historical records is as important as their existence. Immutable backups use WORM (Write Once Read Many) storage technology and cryptographic verification to ensure records cannot be altered after creation — a direct requirement for regulatory audits and fraud investigations.
Financial institutions that cannot produce unaltered audit trails face significant regulatory exposure. The FFIEC Business Continuity Management booklet advises maintaining offline, air-gapped, or immutable copies of critical data to protect against ransomware that compromises both production environments and online backups simultaneously.
Audit and Forensic Capabilities
Regulators expect comprehensive logs of who accessed what data, when backups were created and verified, and how data was restored — all stored in tamper-evident formats. These logs must be producible during regulatory examinations.
The cost of gaps in this capability is concrete. The DBS Bank incident in Singapore resulted in SGD 930 million in additional regulatory capital after MAS identified deficiencies in incident management and recovery processes following a 39-hour service disruption.
Building a Disaster Recovery Plan: RTO, RPO, and Business Continuity
Defining RTO and RPO
RTO (Recovery Time Objective) is the maximum acceptable downtime before systems must be restored. RPO (Recovery Point Objective) is the maximum acceptable data loss measured in time. Both metrics must be defined for each system tier before selecting backup technology, not after.
The RBI's 2023 Master Directions explicitly mandate that regulated entities "should prioritise achieving minimal RTO and a near zero RPO for critical information systems," setting a high bar for Tier 1 financial systems.
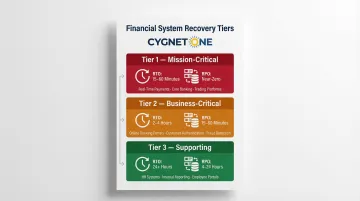
System Tiering for Financial Institutions
| Tier | Systems | RTO | RPO | Examples |
|---|---|---|---|---|
| Tier 1 — Mission-Critical | Payment processing, core banking, trading platforms | 15–60 minutes | Near-zero | Real-time payments, securities trading, ATM networks |
| Tier 2 — Business-Critical | Customer service portals, reporting dashboards, CRM | 2–4 hours | 15–60 minutes | Online banking portals, customer support systems |
| Tier 3 — Supporting | Internal tools, archival databases, dev environments | 24+ hours | 4–24 hours | HR systems, document management, test environments |
Core Components of a Financial DR Plan
Once tiers are defined, each must map to a documented recovery plan. A complete DR plan covers:
- Assign disaster declaration authority, recovery leads, and stakeholder communication owners upfront
- Write step-by-step recovery procedures for each tier — not high-level summaries, but technically actionable instructions
- Prepare communication templates for regulator notifications, client updates, and internal coordination before an incident occurs
- Identify a geographically separate DR site or cloud failover environment for each critical system
- Document escalation paths for all third-party vendors and service providers with SLA commitments
Testing Is Non-Negotiable
The RBI is highly prescriptive on testing frequency — regulated entities must conduct "at least half-yearly" full-scale DR drills for critical systems, covering "at least a full working day (including Beginning of Day to End of Day operations)."
Test results must be documented for regulatory review. Treat each drill as a gap-finding exercise: update procedures based on findings before the next cycle, not as a checkbox to satisfy an audit.
5 Best Practices for Financial Data Backup & Disaster Recovery
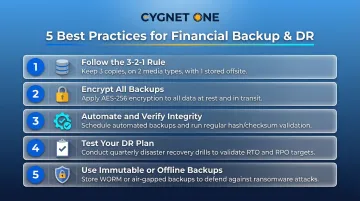
Follow the 3-2-1 Backup Rule
The 3-2-1 rule means maintaining three copies of critical data — one primary plus two backups — stored on two different media types, such as on-premises storage plus cloud, with at least one copy offsite. This protects against localized failures like hardware malfunction or ransomware, and regional disasters like floods or power grid outages.
Implementation checklist:
- Maintain production data plus two independent backup copies
- Use different storage technologies (disk, tape, cloud object storage)
- Store at least one copy in a different geographic region
- Verify all three copies regularly through automated integrity checks
Encrypt All Backups — In Transit and At Rest
Encryption is mandatory for financial backup data. Backup files traveling to cloud storage or offsite locations must be encrypted in transit using TLS 1.2 or higher. Stored copies must be encrypted at rest using AES-256 or equivalent standards. Role-based access controls should limit who can initiate restores, protecting against insider threats.
Automate Backups and Verify Integrity Regularly
Manual backup processes introduce human error, which remains the leading cause of backup failures. Automated backup schedules ensure consistent coverage without relying on individual action. Automated integrity checks and periodic restore tests confirm that backup files are actually usable, not just stored. According to IBM's research, human error was the root cause in 24% of data breaches within the finance sector.
Automated checks confirm individual file health — but they don't tell you whether your full recovery process works end to end. That requires deliberate, scenario-based testing.
Put Your Disaster Recovery Plan to the Test
Documentation without testing creates a false sense of security. Financial institutions should simulate realistic disaster scenarios (ransomware attack, data center outage, accidental deletion) and verify that systems recover within defined RTOs and RPOs. Organizations with high levels of incident response planning and testing saved an average of USD $1.49 million and identified breaches 54 days faster than those with low levels of preparedness.
Implement Immutable or Offline Backups for Critical Data
Store at least one backup copy in an immutable format (WORM storage) or completely offline (air-gapped tape, disconnected storage). This ensures that even if ransomware compromises production systems and online backups, a clean recovery copy remains available. The SAMA Cybersecurity Framework explicitly requires consideration of offline backups in formal backup management strategies.
Frequently Asked Questions
What is the 3-2-1 rule for backing up data?
The 3-2-1 rule means keeping three copies of data on two different storage media types, with one copy stored offsite or in the cloud. This ensures that no single failure — hardware malfunction, ransomware attack, flood, or site-level outage — can destroy all copies simultaneously.
What are the 4 types of data backup?
The four main types are full backup (complete copy of all data), incremental backup (only changes since last backup), differential backup (all changes since last full backup), and cloud/offsite backup (remote copy for geographic redundancy and disaster recovery).
What are the four types of data recovery?
The four primary data recovery methods are restore from backup (recovering from a stored copy), snapshot recovery (reverting to a point-in-time system state), replication failover (switching to a mirrored secondary system), and bare-metal recovery (rebuilding a complete system from scratch onto new hardware).
What is the difference between RTO and RPO in disaster recovery?
RTO (Recovery Time Objective) is the maximum time a system can be down before it must be restored, while RPO (Recovery Point Objective) is the maximum amount of data loss acceptable measured in time. Financial institutions should define both thresholds before a disruption occurs — not during one.
How long should financial institutions retain backup data?
Most regulatory frameworks mandate 5-7 years for financial records. India's GST rules require 6 years (72 months), while SOX mandates 7 years. Institutions operating across multiple jurisdictions must comply with whichever standard is most stringent.
How much should I pay for data recovery?
Costs vary significantly by incident type and severity. According to the Sophos State of Ransomware 2025 report, the mean enterprise remediation cost following a ransomware attack was $1.84 million globally — excluding any ransom paid. Investing in a well-designed backup and DR infrastructure consistently costs far less than a single unplanned recovery event or regulatory penalty.