Introduction
A mid-sized NBFC in Mumbai processes loan disbursals worth ₹50 crore daily. At 2:00 PM on a Tuesday, ransomware locks their core lending system. Payment processing halts. Loan approvals freeze. Regulatory reporting deadlines—GST filings, RBI returns, compliance audits—loom hours away. Within four hours, the institution faces direct revenue loss, potential regulatory fines, and irreversible damage to borrower trust.
This scenario is not hypothetical. In 2024, 65% of financial services organizations were hit by ransomware, with attackers successfully compromising backup repositories in nearly half of those incidents.
For banks, NBFCs, insurers, and payment processors, cloud disaster recovery (cloud DR) is both a technical safeguard and a regulatory mandate. Most institutions, however, treat it as a low-priority IT project until a crisis forces their hand.
This guide covers what cloud DR means for financial services, how it works end-to-end for BFSI institutions, what determines its effectiveness, and where organizations most commonly go wrong.
TL;DR
- Cloud DR restores IT infrastructure, data, and critical financial operations using cloud-based systems after ransomware, outages, or disasters
- For banks, NBFCs, and insurers, it is both a compliance mandate (RBI, DORA, FCA, GLBA, FFIEC) and an operational survival requirement
- Recovery Time Objective (RTO) and Recovery Point Objective (RPO) define how fast systems recover and the maximum data loss an organization can tolerate
- Cloud DR beats on-premises recovery on cost, spin-up speed, multi-region replication, and regulatory fit
- The three most costly mistakes: skipping DR tests, weak access controls, and treating cloud storage as a recovery plan — it isn't
What Is Cloud Disaster Recovery for Financial Services?
Cloud disaster recovery is an organization's strategy and set of tools to replicate, back up, and restore IT systems, applications, and data using cloud infrastructure after a disruptive event: cyberattacks, hardware failures, natural disasters, or human error.
For financial institutions specifically, cloud DR achieves one critical outcome: restoring transaction processing, customer data access, lending workflows, and compliance reporting with minimal downtime and data loss. When a bank's core banking system fails or an NBFC's loan origination platform goes offline, cloud DR determines whether recovery takes hours or weeks.
Cloud DR is often confused with two related concepts, but each serves a distinct purpose:
| Concept | What It Does | What It Doesn't Do |
|---|---|---|
| Backup | Copies and stores data at intervals | Does not restore full operational capability |
| Business Continuity | Covers staffing, communications, manual workarounds | Does not address IT system restoration |
| Cloud DR | Restores IT systems and financial operations after an outage | Does not replace organizational continuity planning |
Understanding this distinction matters for financial institutions: a robust backup strategy alone will not bring your loan origination platform back online. Cloud DR is the piece that bridges data preservation and full operational recovery.
Why Financial Institutions Cannot Afford to Skip Cloud DR
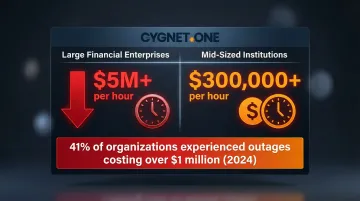
The Financial and Operational Stakes Are Extreme
Financial institutions run real-time payments, loan origination, e-invoicing, GST compliance, and trade finance on systems where even minutes of downtime translate to direct financial loss. The cost figures are stark:
- Large financial enterprises: $5 million+ per hour of downtime
- Mid-sized institutions: $300,000+ per hour
- 41% of organizations experienced outages costing over $1 million (2024 industry analysis)
Beyond revenue loss, each hour of disruption triggers cascading failures — payment processing halts, loan disbursals freeze, customer transactions fail, and regulatory reporting deadlines are missed. Reputational damage compounds with every passing hour.
Regulatory Pressure Is Mandatory and Examinable
Cloud DR is not optional for financial institutions—it is a regulatory requirement subject to inspection and enforcement:
- United States: FFIEC and GLBA mandate formal DR programs with board oversight, testing, and documented recovery objectives
- European Union: DORA (effective January 2025) requires annual DR testing for all ICT systems supporting critical functions, with results reported to competent authorities
- India: RBI Master Directions require semi-annual DR drills for critical systems, with full switch-over to the DR site for at least one working day
- United Kingdom: FCA operational resilience rules require firms to remain within impact tolerances during severe disruptions, with testing records retained for six years
- UAE: CBUAE mandates DR and business continuity plans commensurate with risk profile, with periodic independent review and testing
Non-compliance carries severe consequences. TSB Bank was fined £48.65 million by UK regulators for operational risk failures, including inadequate business continuity planning. VyStar Credit Union paid a $1.5 million penalty and was ordered to implement disaster recovery and failover options after a sustained platform outage. Citizens State Bank in Texas was mandated to test its DR plan within 180 days following regulatory examination findings.
The Threat Landscape Targets Backups Directly
Ransomware attacks now target backup repositories alongside primary systems. In 2024, attackers attempted to compromise backups in 90% of ransomware incidents against financial services organizations, succeeding 48% of the time. Mean recovery costs reached $2.58 million per incident.
Social engineering, third-party vendor failures, and infrastructure outages are rising threat vectors. The 2024 C-Edge Technologies attack in India forced nearly 300 cooperative banks offline when ransomware infiltrated the service provider. The 2023 MOVEit supply chain attack compromised at least 10 U.S. banks through a vulnerability in cloud-synced file transfer software.
On-Premises-Only Recovery Has Real Limits
When flooding, power grid failure, or earthquakes strike, on-premises DR collapses — primary and backup infrastructure can be destroyed simultaneously. Manual recovery processes rarely meet financial SLAs. Smaller institutions and NBFCs, in particular, often lack the internal expertise to execute a full recovery under real crisis conditions without external support.
Compliance Reporting Dependency Creates Direct Finance Risk
Financial institutions running digital tax compliance, e-invoicing, and regulatory reporting pipelines cannot afford data gaps. Any recovery delay creates reconciliation failures, Input Tax Credit (ITC) claim errors, and audit exposure. For institutions processing GST filings, RBI returns, or cross-border VAT compliance, DR is directly linked to finance and tax operations—not just IT uptime.
How Cloud Disaster Recovery Works in Financial Services
Cloud DR works by continuously or periodically replicating an institution's data and system configurations to a cloud-hosted secondary environment. When primary systems fail, operations failover to the cloud environment—ideally within the institution's defined RTO and RPO thresholds.
Understanding RTO and RPO
Two metrics define cloud DR effectiveness:
- Recovery Time Objective (RTO): The maximum acceptable duration of downtime before recovery must occur. For example, core banking must be restored within 4 hours.
- Recovery Point Objective (RPO): The maximum acceptable data loss window. For example, no more than 15 minutes of transaction data can be lost.
Financial services institutions typically demand far tighter RTOs and RPOs than other industries. For crown-jewel systems like real-time payment switches and market-facing trading platforms, authoritative benchmarks target RPOs in the sub-minute to seconds range and RTOs of 5 to 20 minutes. Achieving these aggressive objectives requires Continuous Data Protection (CDP) and automated recovery orchestration.
Types of Cloud DR Approaches
- Backups: Data-only copies stored in the cloud
- Disaster Recovery as a Service (DRaaS): Full IT environment hosted and orchestrated by a third party, offering the best combination of speed, compliance management, and reduced internal burden for most banks and NBFCs
- Point-in-time snapshots: Periodic system state captures
- Virtual DR: Cloud-based replication of virtualized infrastructure
The DRaaS market is projected to exceed $16 billion in 2025, with the BFSI sector as its largest adopter.
Step 1: Risk Assessment and Business Impact Analysis
The process begins by identifying which systems are mission-critical—core banking, loan management, payment processing, compliance reporting—and quantifying the business impact of their failure in financial and regulatory terms. This Business Impact Analysis (BIA) establishes the foundation for RTO and RPO targets.
Across jurisdictions, regulators require institutions to conduct their own BIA and define risk-based recovery objectives. The FFIEC, DORA, FCA, and RBI all mandate this principles-based approach rather than prescribing universal numeric thresholds.
Step 2: DR Plan Design, Replication, and Failover Configuration
Institutions design their DR strategy based on BIA outputs:
- Configure automated data replication to geographically separated cloud regions, ensuring no single natural disaster can destroy both environments
- Set up failover mechanisms for critical applications
- Establish access controls and encryption for replicated data (role-based access with multi-factor authentication)
- Document recovery procedures with clearly assigned roles and responsibilities

When evaluating third-party DR providers, institutions should require:
- Contractual SLAs with uptime guarantees of 99.9% or higher
- Geographic redundancy across multiple data centre regions
- Independent compliance certifications (such as SOC 2 Type III or ISO 27001)
- Transparent incident reporting with defined notification timelines
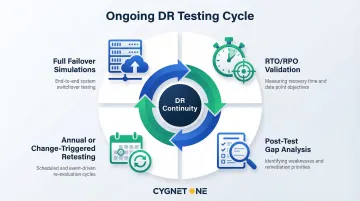
Step 3: Testing, Validation, and Continuous Maintenance
An untested DR plan offers no reliable protection. Financial institutions must conduct scheduled DR drills at minimum annually—often quarterly per regulator expectations—to validate that RTOs and RPOs are actually achievable and to surface gaps before a real crisis.
Industry data reveals significant preparedness gaps:
- 13% of organizations have no DR plan or have never tested one
- Only 27% test more than twice a year
- 58% of servers met their defined recovery SLAs during actual cyber attacks
Regulators are closing in on this gap. DORA explicitly requires financial entities to make DR test results available to competent authorities upon request, and examiners across jurisdictions increasingly review test outcomes during inspections.
Key Factors That Affect Cloud DR Effectiveness in Financial Services
Infrastructure Reliability and Uptime Guarantees
Financial institutions should require contractual SLAs from cloud DR providers that cover three core commitments:
- Defined uptime of 99.9% or higher, tied to the institution's BIA-derived availability targets
- Geographic redundancy across multiple data centre regions to prevent single-location failures
- Transparent incident reporting, including root-cause analysis and resolution timelines
Regulators do not prescribe specific uptime figures, but they do require institutions to define their availability targets and demonstrate the ability to meet them consistently.
Compliance and Certification Alignment
The cloud DR environment must meet the same compliance standards as the institution itself:
- SOC 1/SOC 2 Type II: Demonstrates operational effectiveness of security and availability controls over time
- ISO/IEC 27001: Foundational information security management system certification
- PCI DSS: Mandatory for any systems handling cardholder data
- ISO 22301: Business continuity management system certification specific to resilience
- GDPR adherence: Critical for EU institutions or those handling EU resident data

Institutions using mission-critical platforms for e-invoicing or GST compliance should verify those platforms carry relevant certifications. Cygnet.One, for instance, achieved SOC 1 Type I compliance in 2024 and maintains 99% uptime across infrastructure processing high volumes of financial transactions—demonstrating what compliant financial tech infrastructure looks like in practice.
Data Encryption and Access Control
Data in transit and at rest must be encrypted. Access to DR environments must be role-based with multi-factor authentication. Access rights must be audited regularly and immediately revoked for departing personnel.
DORA explicitly requires that when restoring data from backups, financial entities use ICT systems that are physically and logically segregated from the source system—a mandate for true air-gapped recovery environments.
Scale and Transaction Volume Considerations
Financial institutions processing high transaction volumes—real-time payments, bulk e-invoicing, loan disbursals—require DR infrastructure that can scale to handle peak loads, not just baseline operations. Validate recovery under load during every DR test cycle, not just under minimal traffic conditions.
Institutions should verify that their cloud DR provider can handle the institution's actual transaction throughput during failover scenarios, not just theoretical capacity.
Vendor Dependency and Exit Risks
Institutions must assess whether their DRaaS provider creates lock-in and whether data portability is contractually guaranteed. They should also have a clear answer to a harder question: what happens if the vendor itself goes down? Multi-cloud or hybrid DR strategies reduce this single-vendor exposure.
Contracts must define:
- Exit deliverables, including complete data export in standard, open formats
- Secure data destruction certification
- Provider assistance during transition to alternative solutions
- Tested exit plans validated periodically
Common Misconceptions About Cloud DR in Financial Services
"Cloud Storage Equals Disaster Recovery"
Storing data in the cloud—on a SaaS platform like cloud accounting or loan management software—does not mean the institution has DR. Cloud platforms protect against their own failures, not against user errors, ransomware propagating to synced environments, or misconfiguration.
Institutions need a separate, independent DR layer. That means immutable, air-gapped backups that sit outside the primary cloud environment entirely.
"DR Is an IT Problem, Not a Business Problem"
In financial services, DR directly determines whether loans disburse on time, whether tax filings are submitted, whether customer transactions clear. When DR fails, business leaders—CFOs, COOs, compliance officers—face regulatory and reputational consequences, not just IT teams.
DR is a C-suite and board-level responsibility. Regulators mandate board oversight of BCM and DR programs, and enforcement actions increasingly name senior leadership when gaps are found.
"Testing Once During Setup Is Enough"
DR plans become outdated when systems change, personnel leave, or new regulatory requirements emerge. Many financial institutions discover their recovery plan is broken only when they actually need it. Regulators now actively examine DR test logs and results during audits.
The VyStar Credit Union enforcement action is a clear example: regulators explicitly cited the failure to provide disaster recovery and failover capabilities as a deficiency requiring remediation. A plan that was never retested after a system migration or personnel change is effectively no plan at all.
Ongoing DR testing should cover:
- Full failover simulations (not just tabletop exercises)
- Recovery time validation against documented RTO/RPO targets
- Post-test gap analysis with documented remediation steps
- Annual or change-triggered retesting cycles
When Cloud DR May Not Be the Right Fit
Highly Air-Gapped Regulatory Environments
Institutions operating in highly air-gapped regulatory environments—certain government-owned financial entities with data sovereignty mandates—may face legal constraints on replicating data to third-party cloud infrastructure outside national borders.
India's RBI, for example, has specific data localization requirements. These must be addressed through onshore data copies or customer-controlled encryption keys before any cloud DR architecture is viable.
Network Bandwidth Constraints
Two operational gaps frequently undermine cloud DR before a disaster even occurs:
- Insufficient bandwidth between the primary data centre and cloud provider can push recovery times past RTO thresholds — no matter how well the architecture is designed
- Lack of internal expertise in failover activation means even a sound cloud DR setup will fail under pressure without a qualified managed service partner
Adoption by Default Rather Than Design
Beyond technical constraints, the more common risk is strategic: institutions that adopt cloud DR reactively rather than deliberately. Watch for these warning signs:
- Selecting a cloud DR vendor solely on cost without validating compliance certifications match regulatory obligations
- Institutions that have never tested their DR plan but assume it works
- Organizations that have replicated their legacy infrastructure problems into the cloud without addressing root causes of fragility
Conclusion
Cloud DR in financial services comes down to one question: when disruption hits, how fast can your institution restore operations without breaching regulatory thresholds or losing customer trust?
This guide has covered the core elements that answer that question:
- Define RTO and RPO targets that reflect both business risk tolerance and regulatory mandates
- Select a DR architecture (pilot light, warm standby, or multi-region active-active) matched to your criticality tiers
- Automate failover and test recovery procedures regularly, not just on paper
- Align DR planning with RBI, SEBI, IRDAI, and other applicable compliance frameworks
Understanding these elements at an operational level, not just in a policy document, is what separates institutions that recover in hours from those that face weeks of disruption and regulatory scrutiny. The institutions that treat DR as a living, tested capability are the ones positioned to maintain continuity when it matters most.
Frequently Asked Questions
What is the difference between cloud disaster recovery and business continuity planning for financial institutions?
Business continuity planning covers all operations during a disruption—staffing, communications, manual workarounds—while cloud disaster recovery specifically addresses restoring IT systems and data. DR is a critical component of a broader BCP, focusing on the technical infrastructure that enables business operations to resume.
What are RTO and RPO, and why do they matter in financial services?
RTO (Recovery Time Objective) is the maximum acceptable downtime before systems must be restored; RPO (Recovery Point Objective) is the maximum acceptable data loss window. Financial institutions set tighter targets than most industries because transaction data loss and processing delays carry direct regulatory penalties and revenue consequences.
What regulatory requirements govern disaster recovery for financial institutions?
Requirements vary by jurisdiction—FFIEC and GLBA in the US, DORA in the EU, RBI operational resilience guidelines in India, FCA rules in the UK, and CBUAE frameworks in the UAE. DR plans are examinable items during regulatory audits, with testing results now required to be documented and made available to examiners.
What is DRaaS, and is it suitable for banks and NBFCs?
DRaaS is a model where a third-party provider hosts and orchestrates the full DR environment, including automated failover. Most mid-sized banks and NBFCs find it well-suited to their needs—it reduces operational burden and delivers faster recovery without requiring in-house DR infrastructure.
How often should financial institutions test their cloud disaster recovery plan?
Plan for annual full DR tests and quarterly partial or tabletop exercises at minimum. Regulators now require documented evidence of testing—RBI mandates semi-annual drills with full switch-over for critical systems, and DORA requires annual testing for all functions supporting critical operations. Act on every test's findings.
How does cloud disaster recovery protect against ransomware in financial services?
Effective cloud DR stores immutable, encrypted backups in geographically separated environments that ransomware cannot reach from the primary network. Institutions should verify that their cloud DR environment is logically and physically isolated from primary systems to prevent ransomware propagation—as required by DORA and recommended by CISA for financial institutions.