Introduction
Cloud breaches rarely result from sophisticated attacks. According to Palo Alto Networks' Unit 42 analysis of over 750 incident response engagements, over 90% of breaches were enabled by preventable gaps — misconfigurations, lapses in security coverage, or excessive identity trust.
The AWS Well-Architected Review (WAR) Security Pillar is a structured framework assessment that helps organisations evaluate whether their AWS workloads are designed to protect data, systems, and assets using proven cloud security best practices.
This guide is for cloud architects, CTOs, CISOs, and enterprise engineering teams managing AWS infrastructure. It covers each Security Pillar domain — from identity and access management to incident response — with practical context for reducing risk, strengthening compliance, and hardening your AWS environment against the gaps most breaches exploit.
TL;DR
- The AWS Well-Architected Security Pillar covers identity management, threat detection, infrastructure protection, data security, and incident response
- Reviews surface architectural risks before they become breaches — not after an incident forces your hand
- Five focus areas map directly to AWS services and best practice questions (SEC 1–SEC 10)
- The AWS Shared Responsibility Model defines the boundary: AWS secures the cloud infrastructure; you secure everything you run on it
- Most failures trace back to two habits: running the review once and never revisiting it, and granting overly broad IAM permissions that accumulate unchecked
What Is the AWS Well-Architected Security Pillar?
The AWS Well-Architected Framework defines architectural best practices across six pillars:
- Operational Excellence
- Security
- Reliability
- Performance Efficiency
- Cost Optimization
- Sustainability
The Security Pillar specifically addresses how to protect data, systems, and assets while delivering business value through risk assessment and mitigation.
A Well-Architected Review is a structured evaluation conducted using the AWS Well-Architected Tool — available at no cost in the AWS Management Console. The tool assesses your workload against a set of best practice questions, then surfaces High Risk Issues (HRIs) and Medium Risk Issues (MRIs) ranked by potential business impact.
How the Security Pillar Differs from a Security Audit
The Security Pillar is architectural and forward-looking — it evaluates how a system should be built to resist threats. A security audit is compliance-driven and backward-looking, verifying whether policies were followed. The pillar tells you what to aim for, not exactly how to implement it.
Why the Security Pillar Review Matters for Enterprises
Cloud environments introduce shared, programmable infrastructure that can be misconfigured at scale. The 2025 Verizon DBIR identifies 'Miscellaneous Errors,' including misconfiguration and misdelivery, as a leading cause of data breaches. IBM X-Force's 2025 report highlights that attackers exploit IAM misconfigurations and compromised credentials as primary initial-access vectors.
Understanding the AWS Shared Responsibility Model
AWS secures the physical infrastructure—the "security of the cloud"—including host operating systems, virtualization layers, and data centre facilities. Customers are responsible for "security in the cloud": OS-level security, access controls, data encryption, application security, and incident response. Enterprises that misunderstand this boundary leave critical gaps unaddressed.
Compliance and Regulatory Alignment
Those gaps carry direct regulatory consequences. For organisations in regulated industries, the Security Pillar review maps to the specific controls these frameworks require:
- SOC 2 — logical access, encryption, and monitoring controls
- ISO 27001 — information security management across cloud-hosted assets
- GDPR — data residency, access governance, and breach response obligations
Industries with the highest exposure include BFSI, healthcare, fintech, and high-volume transaction platforms. Cygnet.One's tax and finance platform, which processes 55 million transactions monthly, achieved SOC 2 Type II compliance in 2024—a direct result of applying security controls aligned with these well-architected principles.
The Five Security Focus Areas Explained
The Security Pillar is structured around five operational focus areas: Identity and Access Management (IAM), Detective Controls, Infrastructure Protection, Data Protection, and Incident Response. The review evaluates workloads through 10 best practice questions (SEC 1–SEC 10) mapped to these areas.
Identity and Access Management
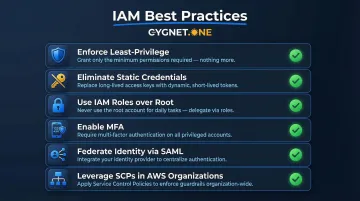
IAM is the foundational layer governing who can do what across all AWS resources. Best practices include:
- Enforce least-privilege policies using granular IAM policies that specify actions, resources, and conditions
- Eliminate long-term static credentials in favour of temporary credentials vended by AWS Security Token Service (STS)
- Use IAM roles instead of root accounts for administrative tasks, reserving root access only for emergency functions
- Enable MFA for all users with console access to add an additional authentication layer
- Federate identity through existing directories using SAML 2.0 for single sign-on (SSO)
- Leverage AWS Organizations and Service Control Policies (SCPs) for centralised access governance across multi-account environments
Detective Controls
Detective controls enable organisations to identify security events through continuous monitoring and logging. Key capabilities include:
- AWS CloudTrail for full API activity auditing and accountability tracking
- Amazon GuardDuty for managed threat detection using machine learning and threat intelligence
- AWS Config for configuration change tracking and compliance validation
- Amazon CloudWatch Events for routing security events into ticketing or SIEM systems
Logs alone are insufficient. Organisations must build analytics and automated alert workflows to detect threats and trigger alerts in time to respond effectively.
Infrastructure Protection
Infrastructure protection prevents unauthorised access to network and compute resources through defence-in-depth controls applied at every layer:
- VPC topology design with careful subnet segmentation, route tables, Network ACLs, and Security Groups
- AWS WAF and AWS Shield for edge protection against web exploits and DDoS attacks
- AWS Systems Manager for hardening OS and application configurations
- Amazon Inspector for automated vulnerability scanning of EC2 instances
When one control fails, the layers beneath it still hold — which is why no single security tool should be treated as sufficient on its own.
Data Protection
Data protection operates across two dimensions: classification and encryption.
Key controls include:
- Data classification: Resource tags, IAM policies, and AWS KMS key access controls determine which data requires which level of protection. Amazon Macie automates sensitive data discovery and classification in S3.
- Encryption at rest: Amazon S3, EBS, and RDS all integrate natively with AWS Key Management Service (KMS)
- Encryption in transit: TLS via AWS Certificate Manager and HTTPS endpoints for all communications
- Tokenisation: For compliance-sensitive data like payment information, tokenisation offers a practical alternative to encryption
Incident Response
Preventive controls reduce risk — they don't eliminate it. The Security Pillar recommends building and testing a response plan that includes:
- Pre-provisioning IAM access for incident response teams with 'break-glass' roles
- Using AWS CloudFormation to spin up isolated "clean room" environments for forensic investigation
- Capturing EBS snapshots for disk state analysis and evidence preservation
- Automating isolation actions via API, such as modifying Security Groups or removing instances from load balancers
These capabilities should be validated through regular game day simulations — testing both the technical runbooks and the team's ability to execute under pressure.
How a Security Pillar Review Works in Practice
A Well-Architected Review for the Security Pillar is conducted using the AWS Well-Architected Tool or through an AWS Well-Architected Partner. The workload owner answers 10 security best practice questions (SEC 1–SEC 10), and the tool produces a prioritised list of High Risk Items (HRIs) and Medium Risk Items (MRIs) with improvement guidance.
Here is how the process unfolds in practice.
Step 1: Define Workload Scope and Context
Before beginning the review, teams must define the workload—the specific set of AWS resources, services, and business functions being assessed. A common mistake is reviewing an entire AWS account rather than a specific, bounded workload, which makes findings impossible to prioritise.
Step 2: Answer the Security Best Practice Questions
During the review session, the team works through each of the 10 security questions:
- SEC 1: How do you securely operate your workload?
- SEC 2: How do you manage authentication for people and machines?
- SEC 3: How do you manage permissions for people and machines?
- SEC 4: How do you detect and investigate security events?
- SEC 5: How do you protect your network resources?
- SEC 6: How do you protect your compute resources?
- SEC 7: How do you classify your data?
- SEC 8: How do you protect your data at rest?
- SEC 9: How do you protect your data in transit?
- SEC 10: How do you anticipate, respond to, and recover from incidents?
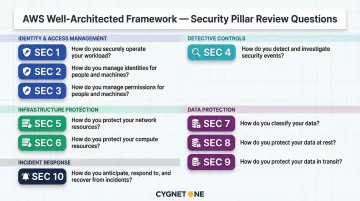
For each question, the reviewer selects which best practices are implemented and which are not. The tool calculates a risk posture based on the responses.
Step 3: Prioritise High-Risk Issues and Build an Improvement Plan
The output is an improvement plan listing HRIs in priority order. Teams should triage HRIs based on:
- Scope of exposure — which data sets or systems are directly at risk
- Time to remediate — whether the fix can be applied within days or requires a longer effort
- Cross-team dependencies — which other services or owners need to be involved
Once triaged, each HRI should be assigned an owner and tracked in the engineering backlog — treated as a live work item, not a one-time report.
Common Mistakes and Misconceptions in Security Pillar Reviews
Treating Reviews as One-Time Exercises
The most common misconception is treating the Well-Architected Review as a one-time certification exercise. The Security Pillar is designed to be reviewed continuously. AWS recommends reassessing workloads after major architectural changes, new service adoptions, or annually at minimum.
Neglecting IAM Hygiene While Focusing on Perimeter Security
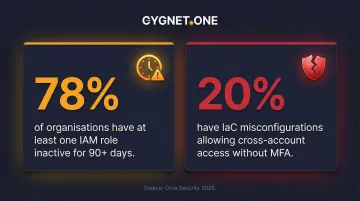
Many organisations focus almost exclusively on perimeter-level infrastructure controls (firewalls, VPCs) while neglecting IAM hygiene and data classification. According to Orca Security's 2025 report, the exposure is widespread:
- 78% of organisations have at least one IAM role inactive for over 90 days
- 20% have Infrastructure as Code misconfigurations allowing cross-account access without MFA
Most real-world cloud security failures trace back to overly permissive access policies or unencrypted sensitive data — not network-level intrusions.
Confusing Reviews with Compliance Certification
Passing a Security Pillar review does not equate to SOC 2 certification or regulatory compliance. AWS describes the review as a "lightweight process that is a conversation and not an audit." The review provides architectural risk visibility; compliance requires additional controls, evidence collection, and third-party validation.
Frequently Asked Questions
What are the pillars of the AWS Well-Architected Framework?
The AWS Well-Architected Framework is built on six pillars: Operational Excellence, Security, Reliability, Performance Efficiency, Cost Optimization, and Sustainability. Each represents a distinct dimension of architectural quality that workloads should be evaluated against.
How is the Security Pillar different from an AWS security audit?
The Security Pillar review is architectural and proactive, assessing how a workload is designed to resist threats. A security audit is typically compliance-driven and retrospective, evaluating whether defined policies were followed. Both are complementary but serve different purposes.
What is the AWS Shared Responsibility Model and why does it matter for the Security Pillar?
AWS secures the physical infrastructure ("security of the cloud"), while customers are responsible for access controls, data encryption, OS configuration, and incident response ("security in the cloud"). Misunderstanding this division is one of the most common sources of security gaps in cloud environments.
How often should an AWS Well-Architected Security Pillar review be conducted?
AWS recommends reviewing workloads at least annually, and after major architectural changes, significant new service adoptions, or a security incident.
What AWS services are most critical to address during the Security Pillar review?
The core services evaluated across the five focus areas include IAM (access control), AWS CloudTrail and GuardDuty (detection), Amazon VPC and AWS WAF (infrastructure protection), AWS KMS (encryption), and AWS CloudFormation (incident response automation).
Do I need an AWS partner to conduct a Well-Architected Security Pillar review?
The review can be self-conducted using the free AWS Well-Architected Tool in the AWS console. However, working with an AWS Well-Architected Partner provides structured facilitation, broader workload context, and access to remediation support, making it especially useful for complex enterprise environments.